The 2025 Cybersecurity Buyers Report
Let's cut to the chase: if you're here you are likely a Cybersecurity Marketer. The question is: why should you be reading this article? Here is a compelling reason: in late 2023 and again in late 2024 ActualTech surveyed our audience of Cybersecurity Buyers for deep marketing insights and produced a report with the Cybersecurity Marketing Society named the Cybersecurity Buyers Report. You can grab your complementary copy at that link. We hope you enjoy the deep insights into cybersecurity marketing.
How to build a strategy that establishes your brand, generates more leads, and drives conversions for your cybersecurity business.
Effective cybersecurity marketing must be a cornerstone of the growth strategy for every service provider in this space.
Demand for cybersecurity services is greater than ever. Security and protection technologies are evolving at a rapid pace, and so are the adversaries trying to break through them. As both become increasingly sophisticated, companies need professional cybersecurity support in order to keep up.
At the same time, the recent emergence of key cybersecurity drivers (largely brought on by the start of the pandemic in 2020) has made this need even more immediate—companies are migrating en masse to the cloud, digital transformation has drastically accelerated, and remote and/or hybrid work environments appear to be here to stay.
Companies in every corner of the business world are seeking out cybersecurity service providers to help them build and maintain a strategy that keeps their infrastructure safe while still allowing them to stay agile and flexible. They’re prepared to invest financially in order to do this.
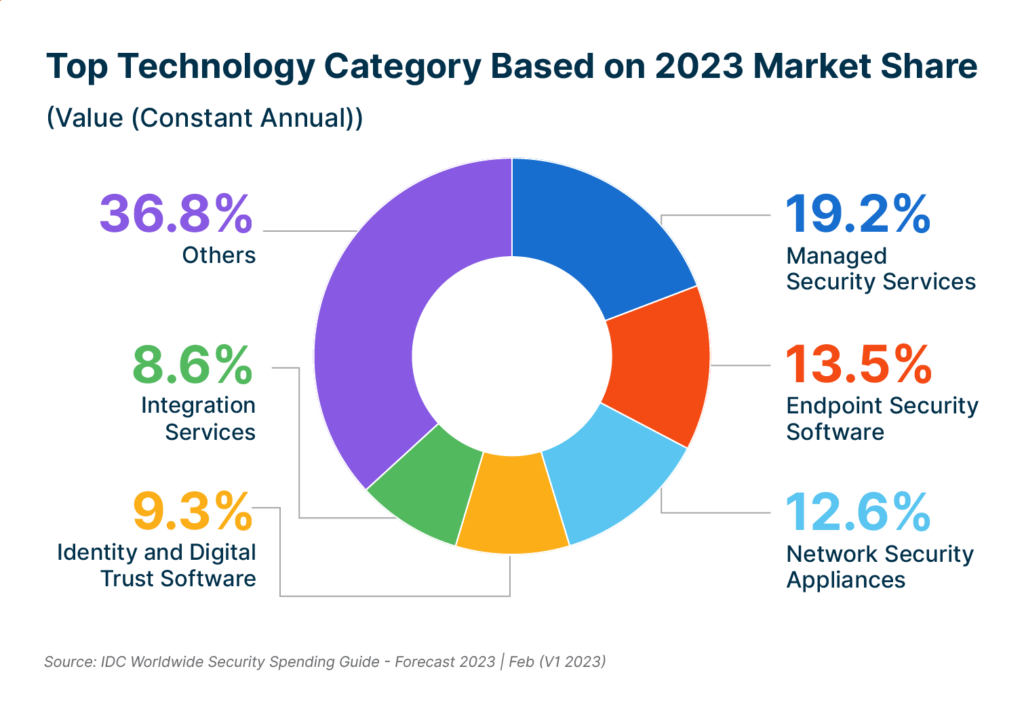
According to the International Data Corporation (IDC), cybersecurity spending will increase 12% this year as compared to 2022, outperforming overall IT spending growth. Cybersecurity services and software account for more than half of that spending.
The key takeaway: There’s a huge opportunity right now for cybersecurity service providers to fill their pipelines with new and high-potential customers—and experience significant growth as a result. To do this, they need to be highly visible and stand out from competitors.
That’s why effective, well-planned cybersecurity marketing is so important. In this guide, we’ll walk through everything you need to know about building a strategy that delivers.
Quick Takeaways
- Cybersecurity marketing buyer personas should focus on knowledge and attitudes related to security issues
- Buyers in the cybersecurity space want to work with brands that demonstrate both subject matter expertise and industry authority
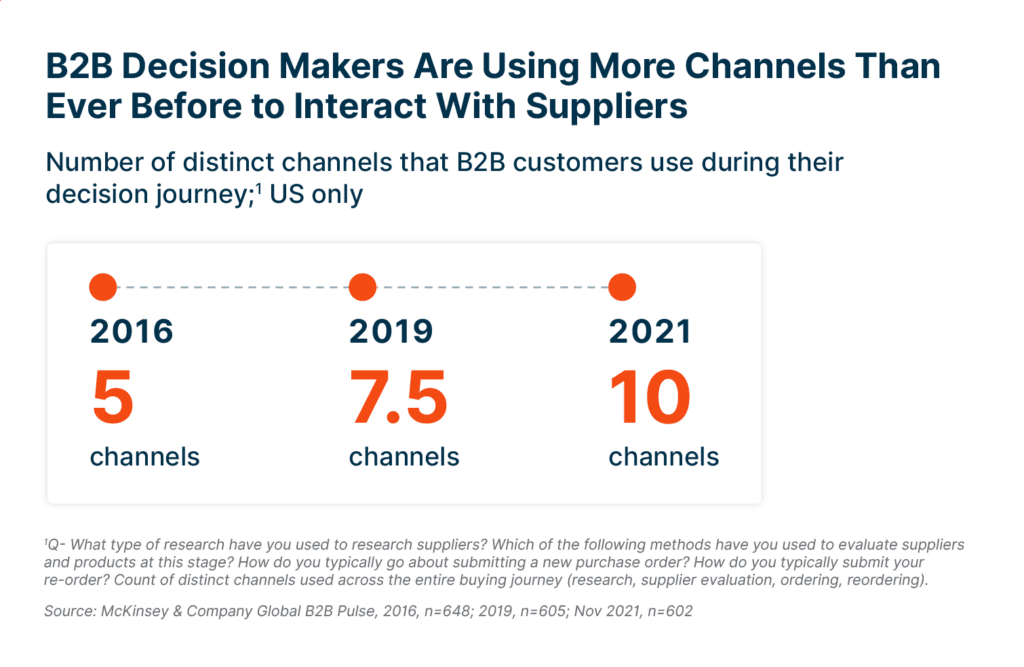
- Today’s B2B buyers engage with 13-plus content assets across 10-plus channels during their purchase journey
- It’s important to avoid highly technical jargon that overwhelms rather than informs your buyers
- Data-driven insights drive better decision making and continuous strategy improvement
- Content marketing is the most cost-effective and results-yielding strategy
- Hiring an agency offers powerful benefits like scalability, access to expertise and technology, proven processes, and 24/7 focus
8 Building Blocks of a Cybersecurity Marketing Strategy
Defined Personas
Buyer personas describe the purchasing decision makers within your target organizations and are typically developed around attributes like position title, level of experience, and salary. In cybersecurity, however, personas are more effective when focused on knowledge and attitude regarding security issues. Examples include:
- The Uninformed: Founders or enterprise heads with little to no cybersecurity knowledge
- The Fretter: Individuals who have had poor experiences with providers in the past and/or are concerned about their ability to implement necessary cybersecurity solutions
- The Skeptic: Decision makers who have never experienced a negative security incident and thus don’t see cybersecurity solutions as relevant to their current needs
The right marketing messages for these (and other) cybersecurity personas vary greatly, so defining each persona is critical to yielding effectiveness measures like more leads generated and higher conversion rates.
Subject Matter Expertise
The technical nature of cybersecurity requires the demonstration of subject matter expertise to your target audiences, especially given that expertise (perhaps even more than other key outsourcing drivers like time and cost) is one of the top reasons companies seek out additional cybersecurity support.
When organizations realize they don’t have enough in-house expertise to execute a confident strategy, they seek out professional organizations to fill the gaps—and they want to hear from your subject matter experts (SMEs) to know that you’re capable.
Partner with your internal SMEs to develop marketing messages, material, and content that shows you have the highest levels of proficiency in your field. It’s effective to include names and faces of your experts where it makes sense (for example, as the author of a blog post or the host of a webinar) to humanize your marketing outreach and make it more relatable.
Industry Authority
Authority and expertise are often discussed interchangeably, but there’s a key difference that’s important to keep in mind for your cybersecurity marketing strategy: positioning.
To be more specific: Expertise can exist in your marketing strategy without actually contributing to your brand’s industry authority. To ensure it translates to authority in your space, you need to apply expertise to the right topics and amplify it on the right channels.
Here are a few ways to do it:
- Use SEO research tools to identify topics your audience cares about
- Research competitor content (and create your own/better versions)
- Build visibility on the channels your audiences use most
- Provide commentary on current cybersecurity events and issues
In the end, authority shows that you don’t just have expertise, you have more expertise than other providers and the right kind of expertise to fulfill your customers’ cybersecurity needs.
Multichannel Engagement
According to McKinsey, B2B buyers interact with potential providers on 10-plus channels throughout their buyer journey. These channels include (but aren’t limited to) websites, social media, search engines, email, online events, demos, phone calls, online chat, landing pages, third-party review sites, ads, and more.
Given that it takes six to eight touches to convert a lead (and even more to convert a sale), meeting your customers on multiple channels where they’re researching is essential to earning their business.
Fortunately, marketing automation technology makes it fairly easy to scale your cybersecurity marketing strategy across multiple channels—think email marketing automation software, social media scheduling software, and content syndication platforms.
Solid Track Record
Social proof—or proof that others are already finding success with your solutions—is important to B2B buyers. In fact, more than 90% of buyers seek out reviews before making a final purchase decision. There are a few ways you can build existing social proof around your brand:
- Publish case studies and client success stories
- Include client testimonials in your marketing materials
- Leverage review sites like G2 or TrustRadius
- Amplify first-party reviews you receive on social media
The easier you make it for potential customers to see your solid track record, the quicker you can earn their trust (and their business).
Relatable Marketing Messaging
While cybersecurity customers want to hire providers with high levels of expertise, they’re often turned off by overly technical jargon and language that’s difficult for them to understand. To make your marketing outreach most effective, develop “layman's terms” messaging that actually informs buyers rather than overwhelming them.
Data-Driven Insights
One of the most significant benefits of today’s highly automated marketing capabilities is data insight. With the right data-driven tools and processes, you can collect data about buyer behavior and cybersecurity marketing performance that can help you continually improve and refine your strategy for better results.
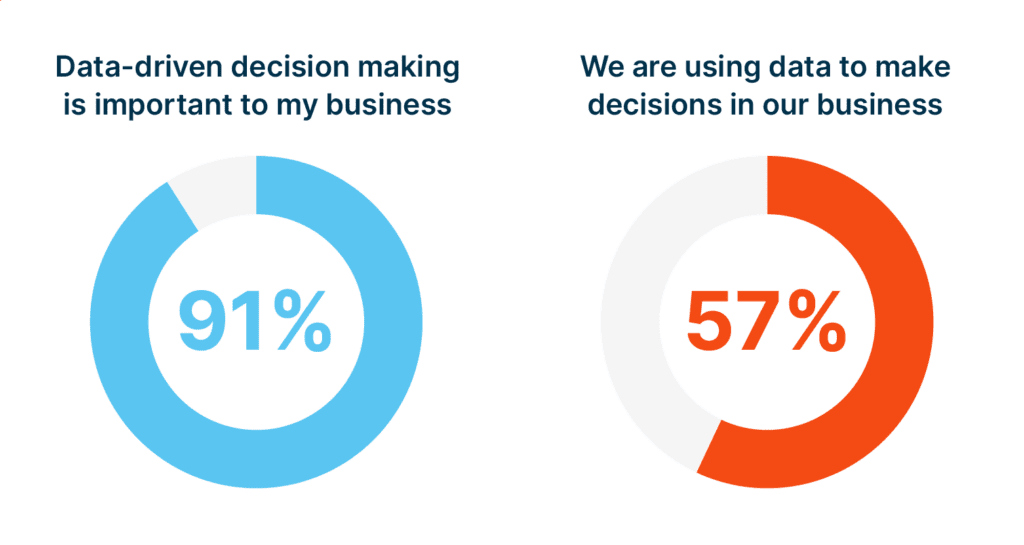
Data-driven marketing can also give you a serious competitive edge. According to research from Wyzowl, 91% of companies know that data-driven decision making is a strategy essential, but only 57% are actually doing it.
Great Content
Buyers complete more than half of their research independently before they ever reach out to potential providers directly. To boot, throughout their buyer journey, they engage with more than 13 pieces of content (created both by vendors and third parties).
You need to be creating great content and sharing it effectively in order for your cybersecurity marketing strategy to yield results that help you grow. In the next section, we’ll dive deeper into how to do it.
Content Marketing: The Cybersecurity Marketing X Factor
Content marketing is both the most cost-effective and highest-performing type of marketing that exists today—it earns companies 3x the leads and costs 62% less than traditional methods. For your cybersecurity marketing strategy to have the biggest impact, content needs to be a central component. Here are a few key steps to content success:
Consistent, Frequent Publishing
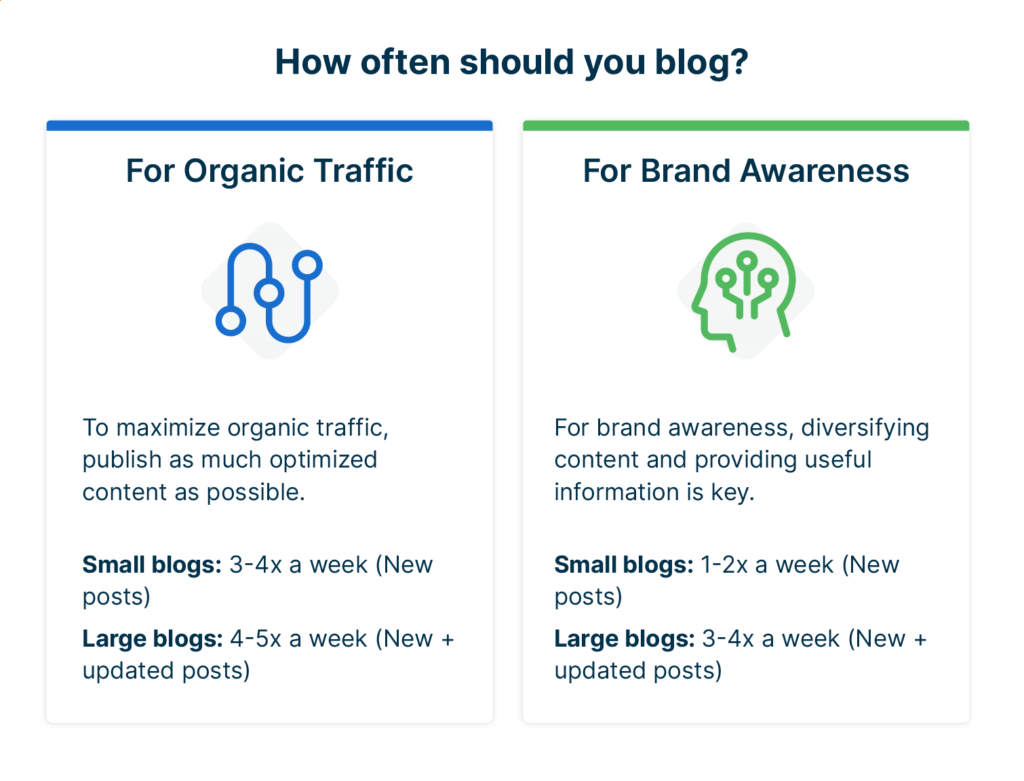
It’s not enough to create a few pieces of content and hope they can earn results. To really make an impact with content marketing, you need to produce high-quality content on a consistent basis—and publish it frequently. For example, HubSpot research found that companies should be publishing up to five blogs per week (depending on company size) to build organic traffic and brand awareness.
The same principle applies to other types of content, too—social media activity, for example, or webinars and other online events. To remain consistent, develop a content creation and publishing plan complete with deadlines and persons responsible that helps you stay on track.
SEO
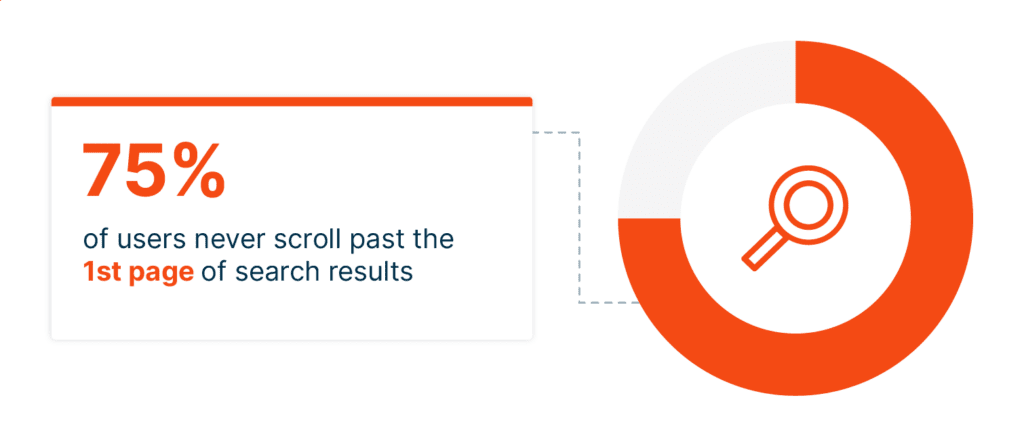
More than 90% of all online experiences start with search engines. It’s the first stop most of your potential buyers are making when they seek out providers. If your content isn’t visible on search engine results pages, you’re likely invisible to your target audiences.
Search engine optimization (SEO) uses keyword research and intentional content structuring to help your content rank highly on Google and other search engines. The result? Your brand shows up first when your buyers search for solutions to their cybersecurity problems. Given that three-quarters of users never scroll past page one of their search results, appearing at or near the top for key search terms is critical to brand visibility.
Multi-Vendor Tech Webinars
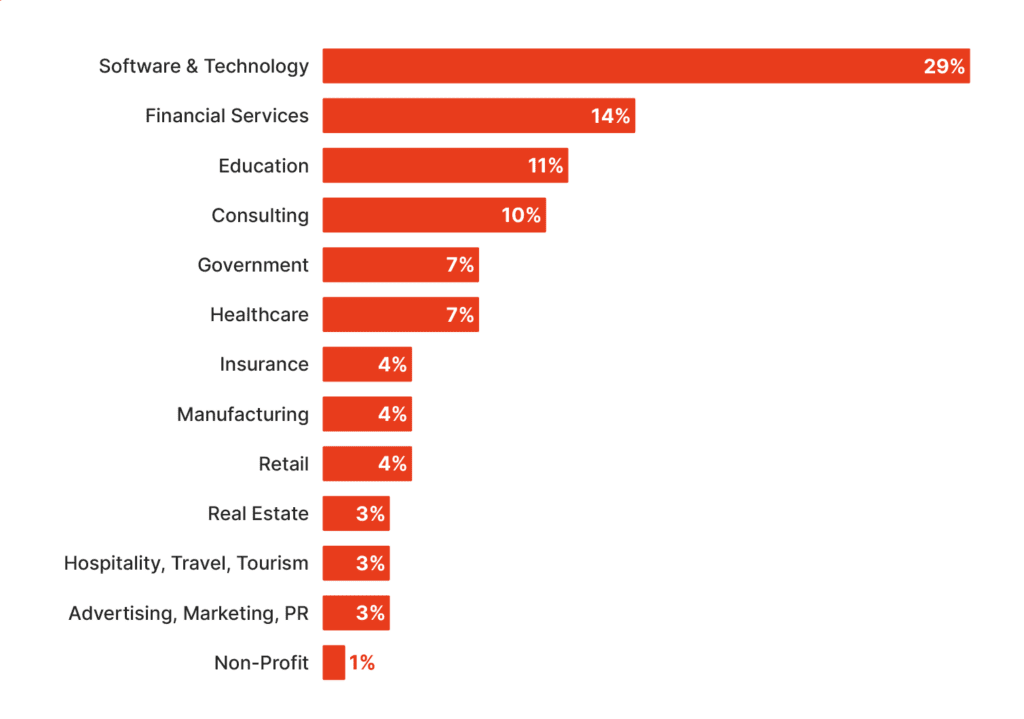
Webinars are one of the most important lead-generating tactics for any industry, but they’re even more important in tech spaces like cybersecurity. In fact, tech accounts for nearly one-third of all webinars held.
Perhaps most effective of all are multi-vendor tech webinars, which position your company next to other providers in your specialty areas so buyers can make accurate comparisons. Multi-vendor webinars also give you an opportunity to directly engage with high-intent buyers and generate leads in the hundreds or even thousands.
For example, a single ActualTech Media-hosted multi-vendor webinar generates 200 to 1,200-plus leads for participating vendors.
Content Syndication
Content syndication for lead generation takes the “passive” out of the traditional version of the process and focuses on getting your content in front of specific, high-fit users that fit your target audience.
Unlike free content syndication, targeted content syndication for lead gen brings in leads you can successfully nurture and reliably convert to sales. The best types of content to use for this purpose are authority-building assets like ebooks, whitepapers, and webinars.
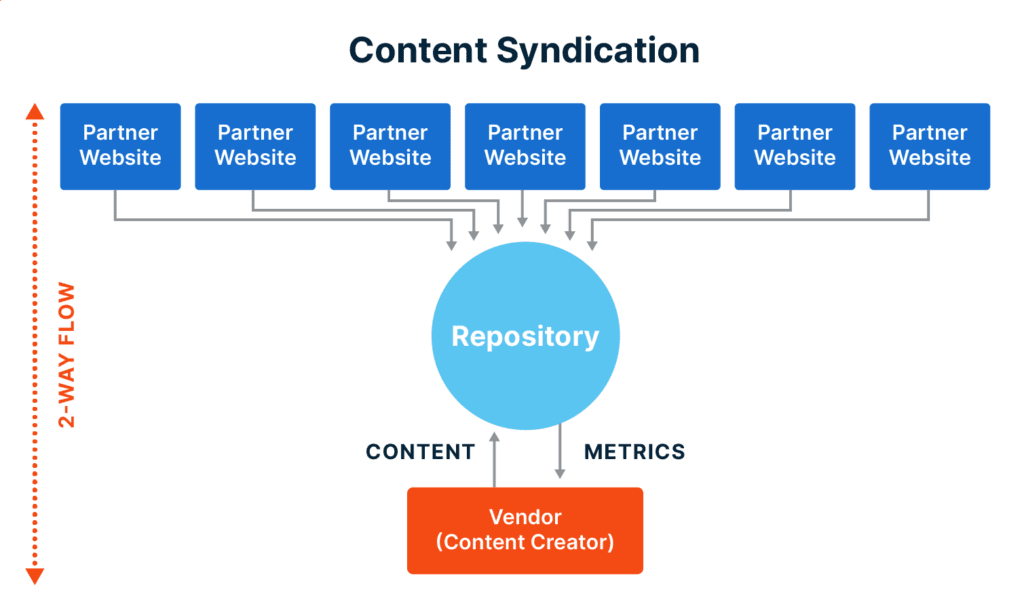
Here’s a visual that shows the flow of content and information during a content syndication campaign:
The key benefit over time is an influx of high-quality leads with true intent to buy and fit with your solutions. The end results are a fuller pipeline, better conversion rates, and increased sales and revenue.
Should You Outsource Parts of Your Cybersecurity Marketing?
By now, you might be thinking it seems impossible to execute a cybersecurity marketing strategy at the scope and scale outlined in this guide. If so, you aren’t alone. Digital marketing in any industry—cybersecurity included—requires time, resources, and overall bandwidth that many organizations can’t maintain in-house.
Many companies choose to outsource parts of their cybersecurity marketing efforts, such as content creation and/or content syndication, to achieve more reliable execution and better results.
Specific benefits of outsourcing include:
- Experience and Expertise: This includes best practices and the latest trends to help your company succeed
- Proven Processes: Processes applied across client strategies and proven to yield the best results
- Tools and Technologies: Access to top marketing automation tools and technologies, many of which integrate with your own systems (such as your CRM)
- Scalability: Ability to scale your efforts up and down as demand dictates (rather than getting stuck with full-time salaries, benefits, and other overhead costs)
- Data-Driven Insights: Frequent performance reporting and audience insights to drive better decisions and continuously improved strategies
- 24/7 Focus: Dedicated teams focused on your marketing efforts all the time
Grow Your Cybersecurity Business with ActualTech Media
Your potential customers are looking for cybersecurity providers with experience, expertise, and strategies proven to work. ActualTech Media can help you put your best foot forward from the very first engagement with your buyers through to lead conversion. We have a long track record of developing marketing materials and strategies that lead to real, measurable results.
Our services include a range of options for creating powerful assets that attract high-quality and high-fit leads for your business. They include:
- Content Creation: We develop custom content designed for your unique company and audience, including blog posts, e-books, videos, and more.
- Multi-Vendor and Custom Webinars: No matter your specific webinar needs, we can help you execute events that engage audiences and generate leads
- Content Syndication: Our campaigns deliver highly targeted leads at affordable CPLs that you can nurture and convert to sales
Interested in learning more about how ActualTech Media can help your business grow? Get in touch with our team to get started.