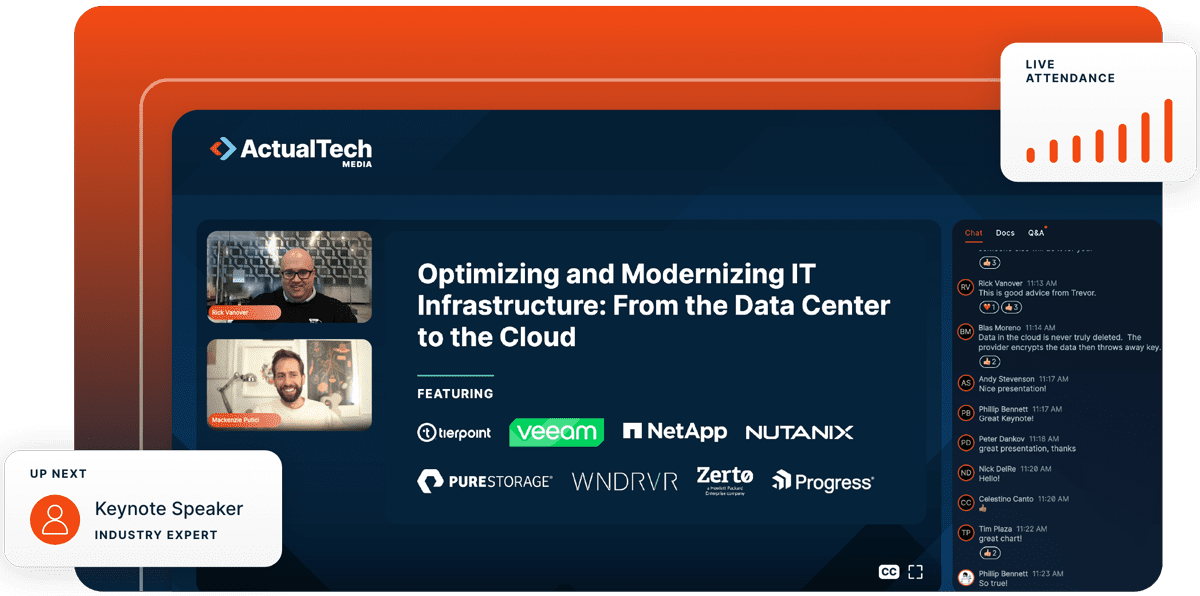
Solutions
B2B Lead Generation Services
Helping technology marketers reach the right buyers, generate demand, and drive pipeline.
Explore All →Who We Serve
Who We Serve
Helping technology marketers connect with the right buyers in competitive markets.
Explore All →Resources